Bypassing the Chinese Firewall
There are multiple ways to bypass the Chinese Firewall, using VPN, anonymous browsers or Tor. But I prefer to use the most simple way, which for me is using an ssh tunnel.
host:~user$ ssh -D 8888 login@myserver.org
(There is also a nice GUI for those who are not familiar with the command line.)
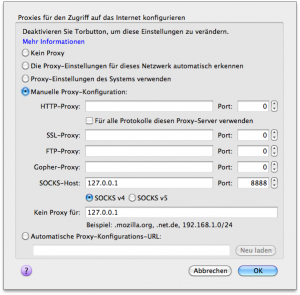
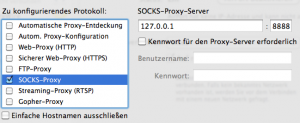
Then I configure my system preferences to use the socks proxy on 127.0.0.1:8888, which can also be done in Firefox Network settings. (see screenshots)
As the Chinese Government also tries to block external sites, such as Youtube and Openleaks, by filtering DNS requests, it’s necessary to filter this too. One could e.g. point them to 127.0.0.1 (in system preferences) and then send through another ssh tunnel:
host:~user$ sudo ssh login@myserver.org -L 53:127.0.0.1:53
(sudo because 53 is a privileged port.)
But actually it’s easier by just hacking the firefox configuration:
… or one can install iodine and tunnel all DNS requests accordingly.
Have phun!